“I consulted Rossmann Repair Group for data recovery services. A new IT client was recently referred to me, because his main computer crashed and his business database went offline as a result. It turned out that the computer crashed because its main storage, a 500 GB Solid State Hybrid Drive, failed. That part was easy - replace it with a new 1 TB SSD and reinstall Windows along with the software he uses. However, the data on the SSHD was critical and would have meant serious problems for his business if he didn't get that back. That's where Rossmann Repair Group came in.”
SSD Data Recovery - NVMe, M.2, and SATA Drive Recovery
From the technician 2 million YouTubers trust. If your SSD is not detected or data became inaccessible, we perform component-level repair instead of canned software clicks; fixing the controller, firmware, or power path so your files can be imaged safely.
How Much Does SSD Data Recovery Cost?
SSD data recovery at Rossmann Group costs $200–$1,500: $200 for simple data copies from functional drives, $250+ for file system repairs, $600 to $900 for circuit board repair, $900 to $1,200 for firmware reconstruction, and $1,200 to $1,500 for advanced board rebuilds. Every case starts with a free evaluation and a firm quote before paid work begins. If we cannot recover your data, you pay nothing.
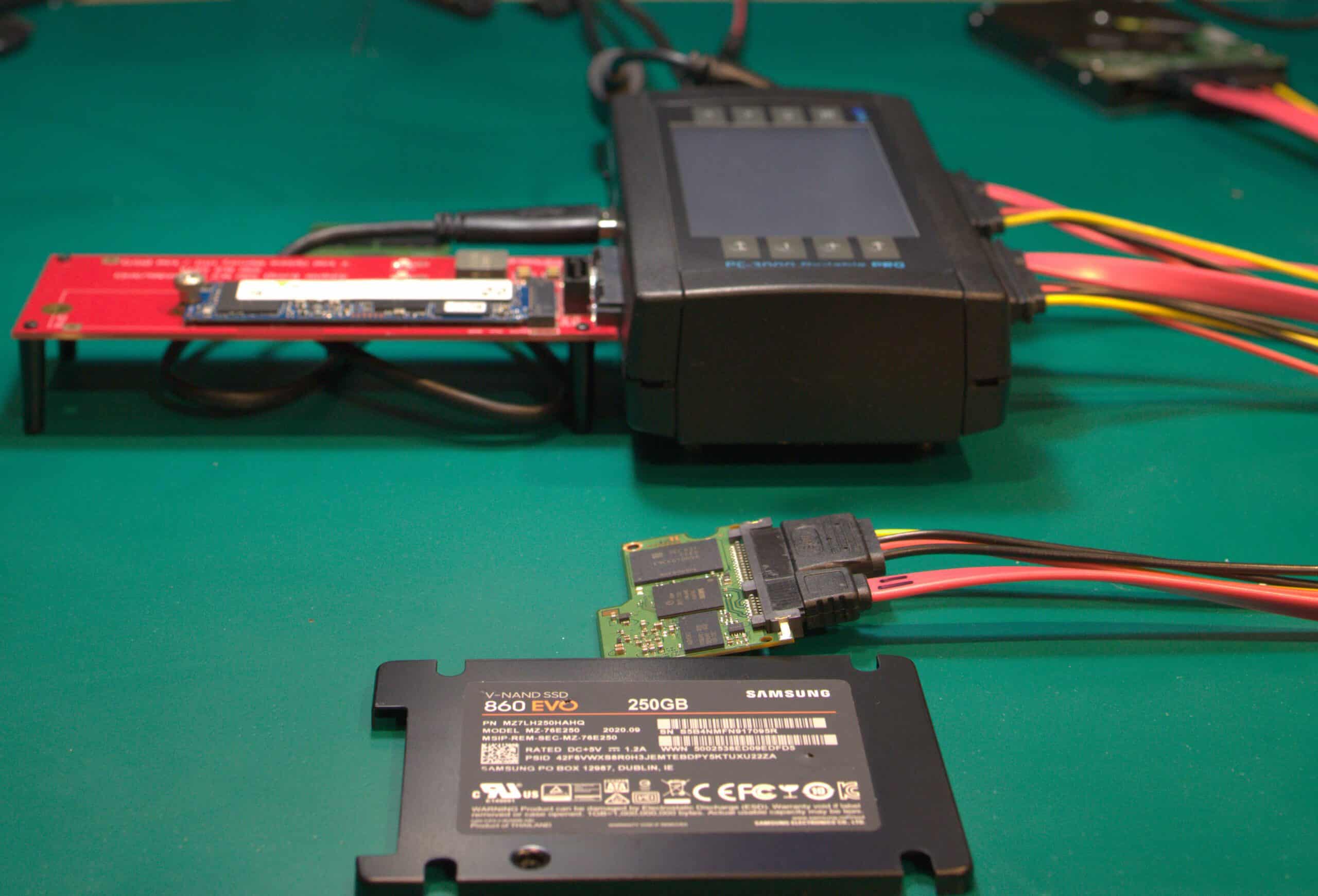
We recover data from NVMe, M.2, and SATA SSDs using PC-3000 Portable III for firmware-level repair and Hakko microsoldering stations for component-level board work. Unlike hard drive recovery, SSD failures involve dead controllers, corrupted firmware translation layers, and shorted power management ICs. Software tools cannot reach data on a drive whose controller is dead. All work is performed in-house at our Austin lab; we do not outsource to third-party labs. Walk-in service in Austin or mail-in from all 50 states.
Drives We Recover From
Validated Equipment. Transparent Process.
The same tools used by top labs, documented on video so you can verify.
Purair VLF-48 Laminar Flow Bench
ULPA-filtered vertical laminar flow with 99.999% efficiency at 0.1-0.3 µm, achieving localized ISO 14644-1 Class 4 equivalent conditions at the work surface. Environmental integrity is continuously monitored down to 0.02 µm sensitivity using the TSI P-Trak 8525 Ultrafine Particle Counter.
PC-3000 Recovery Platform
Industry-standard hardware and firmware-level tools from ACE Lab. Covers head swaps, platter transfers, seized motors, and firmware-level extraction on failed drives.
Every Recovery on Camera
No stock photos of bunny suits. Watch us work on YouTube. 2.49M subscribers see exactly how recoveries are performed, start to finish.


What SSD Recovery Customers Say
“Went in to ask if they could retrieve my SSD from my Surface Pro 4 for me and they gave me a good rate, but was still a bit too expensive for me. So, they let me use their equipment for about an hour until I was able to fish it out myself and recover my data.”
“Sent in a SSD for data recovery for a client of mine. Data was recovered! What else can I say. Thank you.”
“Amazing place! Super friendly and knowledgeable people! I have a LaCie Rugged Pro SSD that stopped mounting. It turns out the enclosure was the problem, not the SSD itself. They helped diagnose the issue and offered solutions—all free of charge. Great experience, and I highly recommend them! 😊”
What is SSD Data Recovery?
SSD data recovery is the process of extracting inaccessible files from solid-state NAND flash memory when the drive's controller, firmware, or electronics have failed. Unlike hard drive recovery, SSD recovery requires board-level electronics repair: microsoldering failed components, reprogramming corrupted firmware through PC-3000, or repairing the power delivery circuit so the controller can power on and serve its data. Software tools cannot reach data on a dead controller.
The failure is in the controller or the board, not in the NAND flash cells where your data lives. The data persists; the path to it is broken. Restoring that path requires component-level electronics work, not software scans.
SSD recovery methods include:
- Logical recovery: Repairing corrupted file systems, rebuilding lost partitions, and carving deleted files from drives where the controller is still functional and TRIM has not unmapped the target blocks
- Firmware recovery: Forcing the controller into safe/diagnostic mode via PC-3000, injecting a working firmware loader, and rebuilding the flash translation layer (FTL) so the drive can map and serve its data again; common on SATAFIRM S11 and other Phison/Silicon Motion controller failures
- Hardware-level recovery: Component-level microsoldering to repair original controller power circuitry, replace shorted PMICs, or inject factory-mode firmware loaders to bypass failed controllers; perform board trace repair for surge-damaged or liquid-damaged drives; and chip-off NAND extraction for unencrypted drives as a last resort when the PCB is destroyed beyond repair
Last updated: March 2026
At a Glance
- $Cost: $200 for simple copies, $250–$1,500 for recovery (firm quote after free evaluation)
- Equipment: PC-3000 Portable III, FLIR Thermal Cameras, Hakko microsoldering stations
- Guarantee: No data recovered = no charge
SSD Data Recovery Pricing
Honest ranges so you can budget without a sales call. Free evaluation and a firm quote before any paid work begins. If it turns out easier than expected, you pay less; not a flat "worst-case" tier. If we cannot get your data, you pay $0 (optional return shipping only). See all service pricing.
Simple Copy
Low complexityYour drive works, you just need the data moved off it
$200
3-5 business days
Functional drive; data transfer to new media
Rush available: +$100
File System Recovery
Low complexityYour drive isn't showing up, but it's not physically damaged
From $250
2-4 weeks
File system corruption. Visible to recovery software but not to OS
Starting price; final depends on complexity
Circuit Board Repair
Medium complexityYour drive won't power on or has shorted components
$450–$600
3-6 weeks
PCB issues: failed voltage regulators, dead PMICs, shorted capacitors
May require a donor drive (additional cost)
Firmware Recovery
Medium complexityMost CommonYour drive is detected but shows the wrong name, wrong size, or no data
$600–$900
3-6 weeks
Firmware corruption: ROM, modules, or system files corrupted
Price depends on extent of bad areas in NAND
PCB / NAND Swap
High complexityYour drive's circuit board is severely damaged and requires NAND chip transplant to a donor PCB
$1,200–$1,500
4-8 weeks
NAND swap onto donor PCB. Precision microsoldering and BGA rework required
50% deposit required; donor drive cost additional
50% deposit required
Hardware Repair vs. Software Locks
Our "no data, no fee" policy applies to hardware recovery. We do not bill for unsuccessful physical repairs. If we replace a hard drive read/write head assembly or repair a liquid-damaged logic board to a bootable state, the hardware repair is complete and standard rates apply. If data remains inaccessible due to user-configured software locks, a forgotten passcode, or a remote wipe command, the physical repair is still billable. We cannot bypass user encryption or activation locks.
No data, no fee. Free evaluation and firm quote before any paid work. Full guarantee details. NAND swap requires a 50% deposit because donor parts are consumed in the attempt.
Rush fee: +$100 rush fee to move to the front of the queue.
Donor drives: A donor drive is a matching SSD used for its circuit board. Typical donor cost: $40–$100 for common models, $150–$300 for discontinued or rare controllers.
Target drive: The destination drive we copy recovered data onto. You can supply your own or we provide one at cost plus a small markup. All prices are plus applicable tax.
Important: Previously messed with or tampered drives may not qualify for "no data, no fee" unless agreed in advance.
Estimate Your SSD Recovery Cost
Select your symptoms and drive type for a preliminary cost range. Final pricing comes after a free evaluation.
What type of SSD do you have?
This determines the recovery method and pricing.
Not sure which type you have? Call (512) 212-9111 and we can help identify it.
What Does My SSD Symptom Mean?
Each SSD symptom maps to a specific hardware failure, recovery method, and cost tier. A drive not detected in BIOS points to a dead controller or shorted PMIC. A drive showing SATAFIRM S11 or 0 bytes indicates firmware translator corruption. A hot drive signals a shorted component drawing excessive current.
| Symptom | Likely Failure | Recovery Method | Price Range |
|---|---|---|---|
| Not detected in BIOS | Dead controller or shorted PMIC | Board-level microsoldering, component replacement | $450–$600 to $1,200–$1,500 |
| Shows SATAFIRM S11 / 0 bytes | Firmware translator corruption | PC-3000 safe mode, translator rebuild | $600–$900 |
| Hot to touch / burning smell | Shorted PMIC or controller component | FLIR thermal imaging, component replacement | $450–$600 |
| Wrong capacity shown | FTL mapping table corruption | PC-3000 Techno Mode, FTL reconstruction | $600–$900 |
| Slow reads / frequent freezes | NAND degradation, ECC threshold exceeded | Multi-pass thermal imaging via PC-3000 | $600–$900 to $1,200–$1,500 |
| Formatted / deleted files | Logical damage (TRIM status determines feasibility) | File system rebuild if TRIM has not unmapped blocks | From $250 |
Prices are starting points. We provide a firm quote after a free evaluation.
Identify Your SSD Failure Type
Select the symptom your SSD is showing. This tool explains what the failure likely is, how we recover from it, and the approximate cost.
Select the symptom that matches your SSD
Each symptom points to a different failure type and recovery method.
How Does SSD Recovery Pricing Compare to Large Labs?
Rossmann Group publishes 5 pricing tiers from $200–$1,500 with a firm quote after a free evaluation. Large national labs quote by phone after a paid evaluation and typically price SSD recovery at $2,000 to $7,000 for the same firmware repairs. The table below reflects published customer reports and competitor pricing pages as of early 2025.
| Provider | Price Range | Pricing Model | No Data, No Fee |
|---|---|---|---|
| Rossmann Group | $200–$1,500 | 5 published tiers with exact prices, firm quote after free evaluation | Yes |
| DriveSavers | $2,000 - $7,000+ | Call for quote, percentage-based legacy model | Varies |
| Ontrack / Secure Data | $800 - $3,000+ | Call for quote | Varies |
Industry estimates based on published customer reports and competitor pricing pages (2024-2025). Actual quotes vary by case.
Large labs price SSD recovery the same way they price hard drive recovery: a wide range quote after a blind evaluation, then the final bill lands at the top of the range. We publish our tiers upfront, give a firm quote after a free hands-on evaluation, and charge nothing if recovery fails. Read the full breakdown of how large lab pricing works.
Why Does Rossmann Publish SSD Recovery Prices?
Rossmann publishes 5 SSD recovery pricing tiers from $200–$1,500 because the cost of a firmware rebuild doesn't change based on who is asking. Every recovery is performed in-house at our Austin lab by the same technicians who diagnose the drive, with flat-rate pricing based on the required repair rather than perceived urgency.
Most data recovery labs hide their pricing behind a phone call because their business model depends on quoting based on how desperate you sound. We publish ours because we are confident in what we charge. A firmware rebuild is a firmware rebuild whether you found us through Google or through a referral. The price does not change based on who is asking.
Every recovery listed on this page is performed in-house at our Austin lab. We do not outsource to a third-party lab. We do not broker your drive to another company. The same technicians who diagnose your SSD are the ones who repair it, image it, and verify the files. You can watch the actual work on Louis's YouTube channel, where we record live recoveries, including the failures. That level of visibility is the opposite of what large labs offer.
Rossmann Repair Group is also one of the most visible advocates for the Right to Repair movement. Louis has testified before the FTC and state legislatures to fight manufacturer restrictions that block independent repair shops from accessing the parts, tools, and documentation needed to fix your devices. That fight is not separate from what we do here. When a manufacturer designs an SSD so that only their authorized service center can access the encryption keys, that is a repair restriction. We work around it with engineering, not permission.
Can Data Be Recovered From a Dead SSD?
Yes, in most cases. A dead SSD usually means the controller has failed, the firmware translation layer is corrupt, or a power management IC has shorted. None of these conditions erase the data in the NAND flash. Flash cells hold charge without power. The data persists even when the controller cannot read it.
A dead controller does not mean dead data. The failure blocks the path to the NAND; it does not wipe the NAND itself.
For shorted components, we locate the failure with a FLIR thermal camera and replace the damaged IC under a Hakko microsoldering station. For firmware corruption, we force the controller into diagnostic mode via PC-3000 and rebuild the flash translation layer from raw NAND metadata. For controller death, we repair the surrounding power delivery circuit so the original controller can power up and serve its data.
The one scenario where SSD data is permanently gone: hardware-encrypted drives where the controller is destroyed beyond repair. Modern NVMe controllers bind AES-256 encryption keys to unique hardware fuses inside the silicon. If the controller cannot be revived through board-level repair, the keys are lost and the NAND contains only unreadable ciphertext. This is why we focus on repairing the original board rather than attempting chip-off; the decryption chain depends on the original controller functioning.
Is SSD Data Recovery Worth It?
SSD data recovery is worth it when the files are irreplaceable and no backup exists. Business records, research data, project files, and family photos have no replacement cost. If the files exist in cloud storage or a separate backup drive, recovery is unnecessary. Our free evaluation lets you assess that before committing to any payment.
Our SSD recovery pricing ranges from $200–$1,500. A file system rebuild costs From $250. Board-level repair costs $450–$600. Firmware reconstruction costs $600–$900. Before committing, you get a free evaluation and a firm quote. We do not start work until you approve the price. If we cannot recover your data, you pay nothing under our no data, no fee guarantee.
The risk calculation is straightforward: you pay $0 to find out whether recovery is possible, and you only pay if we deliver your files. Compare that to national labs where the same firmware rebuild can cost $2,000 to $5,000 with no published pricing.
How Long Does SSD Data Recovery Take?
SSD data recovery at our Austin lab takes 3 to 8 weeks, depending on the failure type. Firmware repairs (translator corruption, safe mode access, FTL rebuilds) take 3 to 6 weeks. Board-level microsoldering takes 4 to 8 weeks because diagnosis requires FLIR thermal imaging and component-level testing before any soldering begins. A rush option is available to move to the front of the queue.
NAND degradation cases with multi-pass read retries and thermal stabilization take 4-8 weeks, as each pass requires adjusted voltage thresholds and cooling periods between reads. We provide a time estimate alongside the price quote after the free evaluation. A +$100 rush fee to move to the front of the queue is available to move to the front of the queue. If your case is time-sensitive, mention that when you ship the drive; we prioritize urgent cases.
Why Can't Software Recover a Dead SSD?
Software recovery tools require a functioning controller to access NAND flash memory. When the SSD controller fails, the drive does not enumerate in the operating system. No software on earth can reach flash it cannot see. Retrieving files requires component-level board repair to restore power to the original controller, then imaging through PC-3000.
Three hardware conditions make software recovery impossible on SSDs: a dead controller, TRIM-erased blocks, and hardware encryption without the original controller intact.
Dead Controller
Software requires a functioning controller to communicate with the drive over USB, SATA, or NVMe. If the controller is dead, the drive does not enumerate. No interface, no access, no recovery path for any software tool.
TRIM Erasure
When you delete files on an SSD, the operating system sends a TRIM command. The controller marks those blocks as invalid and returns zeroes to any read request. Software cannot access data the controller has logically unmapped. This is the opposite of hard drives, where deleted files persist until overwritten.
Encrypted NAND
Modern SSD controllers encrypt all data at rest using AES-256. The encryption key lives inside the controller. Even if you desolder the NAND chips, without the controller's key the raw data is unreadable ciphertext.
Already tried software? If your SSD is not detected in BIOS, software was never going to work. Read the full comparison of software vs professional recovery, or send the drive for a free evaluation.
Software SSD Repair vs. Board-Level SSD Repair
The top search results for "SSD repair" recommend running CHKDSK /f /r, updating firmware through manufacturer dashboards, or using third-party partition managers to "fix bad sectors." These methods address logical file system corruption on a drive whose controller is alive and responding. When an SSD fails from a shorted PMIC, a dead controller IC, or degraded NAND that has exhausted its spare block pool, no software command reaches the flash memory. The controller is the sole gateway, and it is offline.
SSD repair for data recovery is component-level board work: locating a shorted capacitor with a FLIR thermal camera, replacing the failed part under a Hakko microsoldering station, and stabilizing the controller long enough to image the NAND through PC-3000 Data Extractor. Running CHKDSK on a drive with degraded NAND forces intensive write operations that overwrite file system metadata needed for a clean data extraction, and forcing a failing controller to continuously map these new writes can trigger a catastrophic failure of the flash translation layer. The partition manager "bad sector repair" tools that competitors promote cannot rejuvenate physically worn floating-gate transistors; by the time the OS reports bad sectors, the drive's internal spare block pool is already exhausted.
If your SSD is detected with correct capacity and responds to read commands, software tools may help. If the drive shows 0 bytes, reports a wrong model name, gets hot on contact, or is invisible to BIOS, the failure is electronic. Power it off and request a free evaluation. We provide a firm quote under our no data, no fee guarantee before any paid SSD repair work begins.
When to Use Recovery Software vs. When to Ship to a Lab
The failure mode determines the recovery path. If the SSD controller is alive and the drive reports its correct capacity to the operating system, software tools can scan the file system and recover data without opening the case. If the controller is dead, the firmware is corrupt, or the drive is not detected in BIOS, no software can reach the NAND. Board-level repair comes first; imaging comes second.
Scenarios Where Recovery Software Works
Tools like Disk Drill, EaseUS Data Recovery Wizard, and PhotoRec are effective when the hardware is healthy and the loss is logical.
- Accidental Deletion with TRIM Disabled
- If TRIM is inactive (external USB enclosures, some Linux configurations, older macOS without
trimforce enable), deleted file data remains on the NAND until overwritten by new writes. Software scans the raw blocks and rebuilds file signatures. Once TRIM has executed, those blocks return zeroes and software recovery is not possible. - Formatted Partition on a Healthy Drive
- A quick format destroys the file table but leaves underlying data intact. If no new data has been written and TRIM has not unmapped the blocks, software can reconstruct the partition map and recover files. Full formats on SSDs trigger TRIM across the entire volume, making recovery impossible after completion.
- Drive Recognized by OS with Correct Capacity
- If the SSD appears in Disk Management (Windows) or Disk Utility (macOS) with its correct model name and full capacity, the controller and flash translation layer are functional. The failure is at the file system level. Software can target logical corruption without hardware intervention.
Scenarios That Require Lab Recovery
When the hardware path between NAND and host is severed, software has no interface to work with. Running recovery tools on a drive in these states forces the controller to retry reads on failing NAND, accelerating degradation.
- Controller Failure: Drive Not Detected in BIOS
- A dead controller or shorted PMIC prevents the drive from enumerating. No operating system sees it; no software can address it. We locate the short with a FLIR thermal camera, replace the failed component under a Hakko FM-2032 microsoldering iron, and restore power to the controller before imaging through PC-3000. Cost: $450–$600 to $1,200–$1,500.
- Firmware Corruption: Drive Stuck in Safe Mode
- When the flash translation layer corrupts, the SSD may report as SATAFIRM S11, show 0 bytes, or display the wrong model name. The controller cannot map logical addresses to physical NAND pages. PC-3000 SSD forces the controller into diagnostic mode and rebuilds the translator from raw NAND metadata. Cost: $600–$900.
- NAND Degradation: Accumulating Read Errors
- As NAND cells wear past their rated program/erase cycles, read errors exceed the controller's ECC correction threshold. Software receives corrupted data or timeout errors. Lab recovery uses PC-3000's Read Retry with adjusted voltage thresholds and thermal stabilization to shift sensing margins back into readable range. Cost: $600–$900 to $1,200–$1,500.
- TRIM-Erased Data: Physically Zeroed Blocks
- After TRIM executes, the controller returns zeroes to all read requests for the affected addresses. Software sees empty space. If the drive died from a hardware failure before TRIM completed, the data may still be on the NAND. Otherwise, TRIM erasure is permanent regardless of method; neither software nor lab work can retrieve zeroed blocks.
- Encrypted Controller: AES-256 Key Bound to Dead Silicon
- Modern SSD controllers encrypt all data at rest with AES-256, binding the media encryption key to hardware fuses inside the controller die. If the controller dies, desoldering the NAND yields only ciphertext. Chip-off is not a viable path. The only recovery option is component-level board repair to revive the original controller so it can decrypt its own storage. Cost: $450–$600 to $1,200–$1,500.
If you are unsure which category your drive falls into, check BIOS first. A drive that appears with its correct model name and capacity is a candidate for software recovery. A drive that is invisible, shows the wrong identity, or gets hot on contact needs lab evaluation. Our evaluation is free, and we provide a firm quote under our no data, no fee guarantee before any paid work begins.
How Does SSD Recovery Work?
SSD recovery restores access to NAND flash by repairing the controller, firmware, or power delivery circuit that failed. The process starts with a free evaluation, moves to component-level board repair or firmware reconstruction, and ends with sector-by-sector imaging through PC-3000.
Detailed step-by-step recovery process below
- 01
Evaluation
Chris diagnoses power rails, controller response, and NAND status. Free quote with realistic odds before any paid work.
- 02
Repair & Imaging
Component-level board repair, firmware reconstruction, or direct NAND reads depending on architecture. Image-first workflow to protect your data.
- 03
Data Return
Files verified, transferred to your choice of media. No data = no charge on qualifying jobs.

A Message from Our Lead Engineer
A Personal Guarantee from Louis Rossmann
The data recovery industry is filled with “flat rate” scams and companies that prey on your panic. I started this business to be the antidote to that.
I have testified before Congress and State Legislatures fighting for your Right to Repair. I have built a YouTube channel with over 2.5 million subscribers by showing our work; honestly and transparently; for over a decade. I am not going to throw away that reputation to make a quick buck on your hard drive.
My promise is simple: If we cannot recover your data, you do not pay a cent.No “attempt fees,” no “clean room fees,” no surprises. You deal with engineers, not salespeople.
Louis Rossmann
Data Recovery Standards & Verification
Our Austin lab operates on a transparency-first model. We use industry-standard recovery tools, including PC-3000 and DeepSpar, combined with strict environmental controls to make sure your hard drive is handled safely and properly. This approach allows us to serve clients nationwide with consistent technical standards.
Open-drive work is performed in a ULPA-filtered laminar-flow bench, validated to 0.02 µm particle count, verified using TSI P-Trak instrumentation.
Transparent History
Serving clients nationwide via mail-in service since 2008. Our lead engineer holds PC-3000 and HEX Akademia certifications for hard drive firmware repair and mechanical recovery.
Media Coverage
Our repair work has been covered by The Wall Street Journal and Business Insider, with CBC News reporting on our pricing transparency. Louis Rossmann has testified in Right to Repair hearings in multiple states and founded the Repair Preservation Group.
Aligned Incentives
Our "No Data, No Charge" policy means we assume the risk of the recovery attempt, not the client.
Technical Oversight
Louis Rossmann
Louis Rossmann's well trained staff review our lab protocols to ensure technical accuracy and honest service. Since 2008, his focus has been on clear technical communication and accurate diagnostics rather than sales-driven explanations.
We believe in proving standards rather than just stating them. We use TSI P-Trak instrumentation to verify that clean-air benchmarks are met before any drive is opened.
See our clean bench validation data and particle test videoRecent SSD Recovery Cases
Samsung 980 Pro 2TB
Controller Short
Dead to system. FLIR showed thermal runaway on the PMIC. Replaced the shorted capacitor and reflowed the power management IC. Drive booted in PC-3000. Full image, 100% of files recovered.
Full recovery
Kingston A400 480GB SATA
SATAFIRM S11 / 0 Bytes
Drive enumerated with wrong model string and zero capacity. Firmware translator was corrupt. Rebuilt the translator and service area modules via PC-3000 SSD utility. Full file system intact.
Full recovery
Apple M1 MacBook Pro
Liquid Damage
Coffee spill killed the logic board. Ultrasonic cleaning, then rebuilt corroded power rails and replaced two shorted capacitors near the SSD power path. Board booted, Secure Enclave decrypted, data extracted through the repaired board.
Full recovery
Crucial MX500 500GB
Degraded NAND
Drive dropped offline after years of heavy writes. Service area partially unreadable. Placed in safe mode via PC-3000, rebuilt translator from surviving metadata, multi-pass read with thermal optimization.
Near-complete recovery
MacBook Air (Soldered SSD)
SSD Shorted & Smoked
Board-level short caused the SSD controller area to overheat and smoke. Thermal imaging located the failed component. Replaced the shorted IC, restored power path, and imaged the soldered NAND through the repaired board. Watch this case.
Full recovery
Lab Environment Verification
SSD recovery requires a clean bench for precision micro-soldering, not an entire cleanroom. Our Laminar Flow Bench maintains ISO 14644-1 Class 4 equivalent air quality at the work surface.
Recent Recoveries
| Date | Drive / Controller | Issue | Tool | Result |
|---|---|---|---|---|
| Feb 2026 | 2TB Phison E12 | Firmware Translation Layer Corruption | PC-3000 Portable III | Full Recovery |
| Feb 2026 | Samsung 870 EVO | Degraded NAND / Bad Blocks | PC-3000 Read-Retry | 98% Recovered |
| Jan 2026 | Silicon Motion SM2258XT | Controller Lockup | PC-3000 Firmware Reconstruction | Full Recovery |
Watch Real SSD Recoveries
Full walkthrough: save mode activation, firmware injection, translator rebuild, and heat-assisted NAND reading on a failing NVMe drive.
Video Summary
This video walks through a complete NVMe SSD recovery case from initial diagnosis to final file extraction. The drive fails to enumerate in the operating system, showing no capacity and no model string. The PC-3000 Portable III with its PCIe SSD adapter communicates with the failed controller at the hardware level, bypassing the normal host interface entirely. The first step is placing the controller into Techno Mode, a diagnostic state that halts normal controller logic and allows the recovery tool to issue low-level vendor commands. From there, PC-3000 reads the service area modules where the firmware translation layer (FTL) is stored. Several FTL modules are corrupt, preventing the controller from mapping NAND addresses to logical block addresses. The repair involves injecting a working firmware loader and rebuilding the translator using surviving metadata from the NAND chips. Because the NAND cells have accumulated write wear and some pages show charge retention loss, standard reads return ECC errors. The video demonstrates the heat-assisted read technique: controlled warming of the NAND package shifts the voltage threshold distributions back into readable range, reducing uncorrectable bit errors enough for the ECC decoder to reconstruct the data. After the translator rebuild, the drive becomes accessible through the PC-3000 imaging pipeline. The case shows why controller failure on an NVMe drive does not mean permanent data loss, provided the NAND itself still holds valid charge and the service area metadata can be reconstructed.
MacBook Air SSD thermal failure: damage assessment, short circuit detection, and soldered NAND recovery feasibility.
Video Summary
This video covers a MacBook Air that arrived with visible thermal damage: the SSD controller area on the logic board had shorted, drawing excessive current, and the area around the NAND package showed heat discoloration. The SSD is soldered directly to the logic board with no removable module. The diagnosis begins with a FLIR thermal camera to locate the shorted component before applying power. The failed IC is identified near the NAND power rail. Repair involves desoldering the failed component under a Hakko microsoldering station, fitting a matching donor part, and rebuilding the damaged board traces adjacent to the pad. Because this is an Apple Silicon MacBook, the NAND is encrypted by the Secure Enclave inside the M-series SoC. Chip-off recovery is not viable: desoldering the NAND packages produces only AES-256 ciphertext with no accessible key. The only path to the data is restoring enough board functionality that the Secure Enclave can power on and decrypt in place. After component replacement and trace repair, the board powers on. The Secure Enclave initializes, the APFS volume mounts, and the data is extracted through the repaired board. The case illustrates why board-level microsoldering capability is required for Apple T2 and M-series SSD recovery, and why labs without soldering capability cannot handle these cases.
Why Choose Rossmann
Component-level diagnosis
Microscope work, BGA rework, board-level repair; real component-level diagnosis, not just software.
YouTube transparency
We show the work, not stock photos. Founder Louis Rossmann is a Right-to-Repair leader.
In-house only
Your device stays in our Austin lab. No outsourcing, no middlemen.
No BS pricing
Clear ranges, free evaluation, no data = no charge.
Can You Recover the Data Yourself?
Software recovery tools work only when the SSD controller is alive and the drive reports its correct capacity to the operating system. If the controller is dead, the drive doesn't enumerate, and no software can reach the NAND flash. Board-level repair is required to restore access before any data can be imaged.
Software recovery tools (Recuva, R-Studio, Disk Drill) work by scanning the file system through the operating system. They require the OS to see the drive. If the SSD controller is dead, the drive does not enumerate, and no software on earth can reach the NAND. There are no spinning platters to image with a sector reader; the controller is the only gateway to the flash memory. A dead controller means zero access at the software level.
| Scenario | Software Tools | Board-Level Lab |
|---|---|---|
| Controller dead | No access. Drive not detected by OS. | Component-level board repair restores access for imaging. |
| Files deleted (TRIM ran) | Blocks logically unmapped. Unrecoverable. | Unrecoverable. TRIM is permanent. |
| Firmware corruption (SATAFIRM S11) | Drive shows wrong identity. Software cannot connect. | PC-3000 rebuilds translator and service area modules. |
| Hardware-encrypted drive | Ciphertext only, even if drive is detected. | Repair original controller to preserve decryption chain. |
| Liquid damage | Drive shorted. Do not power on. | Ultrasonic cleaning, component replacement, then imaging. |
| NAND degraded | ECC errors cause read failures and corrupted output. | Multi-pass thermal reads via PC-3000, FTL reconstruction. |
Software tools require a functioning controller and visible drive. Board-level lab work addresses the hardware failure first, then images the data.
Safe to Try
- ✓Open Disk Management (Windows) or Disk Utility (macOS) and check if the drive appears at all, even without a partition
- ✓Try a different USB-to-NVMe or USB-to-SATA adapter; cheap enclosures fail often and mimic a dead drive
- ✓Check BIOS/UEFI detection; if the drive shows its correct model and capacity, the controller is alive and software tools have a chance
Stop Immediately
- ✗Drive gets hot to the touch within seconds of connecting; this indicates a shorted component drawing excessive current
- ✗Burning smell from the drive or enclosure; continued power destroys adjacent NAND chips
- ✗Drive reports as SATAFIRM S11 or shows 0 bytes capacity; the firmware translation layer is corrupt and repeated power cycles risk overwriting the service area
What Happens If You Try DIY Data Recovery on a Failing SSD?
Plugging a failing SSD into a computer triggers automatic TRIM commands, journal replays, and garbage collection that erase data the controller had flagged for deletion. Running CHKDSK or fsck on degraded NAND overwrites the directory structure needed for clean extraction, turning a firmware-level recovery into a fragmented carving job that costs more and recovers less.
Plugging a failing SSD into a computer triggers automatic operations that reduce recovery odds. The OS attempts to mount the volume, replaying its journal and issuing queued TRIM commands. If the controller responds, it begins background garbage collection, physically erasing pages the OS flagged for deletion.
Each of those background operations updates flash translation layer (FTL) metadata distributed across the NAND chips. On a drive with degraded NAND, those writes push worn cells past their ECC correction threshold, corrupting the mapping tables that PC-3000 needs to reconstruct the data.
Running CHKDSK /f /r (Windows), fsck (Linux), or Disk Utility First Aid (macOS) on a physically failing SSD is worse than doing nothing. These utilities detect ECC read timeouts from degraded NAND cells and misinterpret them as logical file system corruption.
CHKDSK responds by deleting corrupted directory index entries, stripping orphaned files of their original paths, and rewriting the Master File Table (MFT) to force the volume to mount cleanly. On a healthy drive, this fixes directory errors. On a drive with failing NAND, it overwrites the original directory structure with a version that references blocks the controller can no longer read, turning a firmware-level recovery into a fragmented data carving job that costs more and recovers less.
Recovery software (Recuva, R-Studio, Disk Drill) is safe only when the SSD controller is alive and the drive reports its correct capacity to the OS. If the drive shows 0 bytes, reports as SATAFIRM S11, gets hot on contact, or is invisible in BIOS, the failure is at the firmware or hardware level. Power it off. Do not install recovery software onto the same drive. Do not let the OS attempt repairs. Ship it to a lab that can access the NAND through the controller's diagnostic interface without triggering background operations. We provide a free evaluation and a firm quote under our no data, no fee guarantee before any work begins.
Have a spinning hard drive instead? Clicking, beeping, or not detected - we do those too. Clean bench, PC-3000, donor parts on hand. We also handle RAID arrays and NAS devices.
What SSD Failure Types Can Be Recovered?
Each failure has its own diagnostic path and repair strategy. Controller failures and firmware corruption are recoverable in most cases. TRIM-erased files on a drive that kept running are not.
Most data recovery labs are built around hard drives. Their tooling is clean rooms, platter swaps, and head stacks. None of that applies to SSDs. An SSD has no platters, no heads, and no spindle motor. When an SSD fails from physical or electronic damage, the fix is component-level electronics repair under a microscope. Labs that lack microsoldering capability send these cases back as unrecoverable. Note: many SSD failures happen without warning. SMART monitoring can catch wear-related failures on SSDs, but controller lockups and firmware bugs bypass SMART entirely.
Controller Failure
Symptoms: not detected, shows 0GB/8MB, instant disconnects, shows as SATAFIRM S11, or runs unusually hot. Common controllers: Phison, Silicon Motion, Marvell, Samsung, SandForce.
Our approach: diagnose PMIC/power rails, replace shorted components, or inject factory-mode firmware loaders to bypass a failed controller. We then use PC-3000 to initialize firmware and image.
Typical outlook: These are usually recoverable. A dead controller doesn't mean dead NAND. Depending on encryption architecture, we replace the controller IC or repair its power path.
NAND / Firmware Corruption
Symptoms: system hangs on access, disk reports odd capacity, partitions vanish after unsafe shutdown/updates.
Our approach: rebuild translator and metadata, direct NAND read if necessary, then extract the data by applying ECC and rebuilding the flash translation layer.
Typical outlook: Good odds when the corruption is logical rather than physical. The data is still on the chips - we just need to make sense of the scrambled map.
Board-Level Repair Techniques
- Power Rail Repair
- A shorted capacitor or blown PMIC (power management IC) kills the drive instantly. We use a FLIR thermal camera to locate the short, then replace the failed component under a Hakko microsoldering station. Common on Samsung 970/980 EVO drives after power surges.
- Controller Failure Recovery
- A dead controller does not always mean dead data. While older architectures sometimes allowed for direct controller transplantation, modern solid-state drives use complex internal mapping that makes simple chip swapping impossible. Instead, we bypass the failed controller by repairing the surrounding power delivery circuitry, correcting localized shorts, or injecting specialized factory-mode firmware loaders via PC-3000 directly into the controller's diagnostic interface to initialize the drive and reconstruct the translation layer.
- Trace and Connector Repair
- Bent M.2 edge connectors, cracked PCBs from drops, and corroded traces from liquid damage all sever the electrical path between NAND and controller. We repair broken traces with jumper wires under magnification and rebuild corroded pads with fresh solder.
- NAND Chip-Off
- Modern NVMe controllers use complex, proprietary error-correction algorithms (LDPC). Because the data is heavily mathematically encoded across the NAND chips, traditional "chip-off" data recovery is often impossible without functioning controller hardware. We focus on advanced logic board repair and firmware manipulation to temporarily revive the original controller, allowing it to decrypt and decode your data natively.
Every SSD repair listed above is temporary: we restore controller functionality long enough to image your data through PC-3000 Data Extractor, then retire the drive. A physically repaired SSD should not be reused as a production drive. The underlying failure (NAND wear, thermal damage, voltage regulator degradation) means the drive will fail again. SSD repair for data recovery is board-level component work to extract files, not a permanent refurbishment.
Liquid damage note: corrosion spreads every hour a wet drive sits unpowered. If your SSD got wet, do not try to dry it with rice or a hair dryer. Ship it to a lab. We ultrasonically clean the board, neutralize corrosion, and assess component damage before applying power.
Troubleshooting Guides
What Do Common SSD Failure Terms Mean?
SSD failures divide into four hardware-level conditions: controller lock, NAND degradation, translation layer corruption, and PMIC failure. Each has a distinct symptom pattern and a distinct recovery path. Understanding which condition applies determines whether recovery is feasible before any work begins.
- Controller Lock
- The SSD controller IC enters a protective state after detecting internal errors, preventing all data access. The NAND retains your files, but the controller refuses to serve them. Recovery requires forcing the controller into a diagnostic mode via PC-3000 or repairing the failed power delivery circuit that caused the lockup.
- NAND Degradation
- Flash memory cells lose their ability to hold charge after repeated program/erase cycles. TLC NAND is rated for roughly 1,000 to 3,000 P/E cycles; QLC NAND for roughly 100 to 1,000. As cells wear, read errors increase until the controller's ECC can no longer correct them. We use PC-3000's Read Retry with adjusted voltage thresholds and thermal stabilization to recover sectors that fail at standard sensing margins.
- Translation Layer Corruption
- The flash translation layer (FTL) maps logical block addresses to physical NAND pages. When this map corrupts from power loss or firmware bugs, the drive appears empty, shows wrong capacity, or reports as SATAFIRM S11. PC-3000 rebuilds the translator tables by scanning raw NAND metadata and reconstructing the address map.
- PMIC Failure
- The power management IC regulates voltage to the controller and NAND. A power surge or voltage spike shorts the PMIC, killing the drive instantly. The NAND is unaffected because flash cells hold charge without power. We locate the short with FLIR thermal imaging and replace the failed PMIC under a Hakko microsoldering station.
What Happens to Deleted Files on an SSD?
When you delete a file on an SSD, the operating system sends a TRIM command that marks those blocks as invalid. The controller returns zeroes to any read request for those addresses, making deleted data inaccessible through software within seconds. Physical NAND erasure follows later during garbage collection, but the controller blocks access the moment TRIM completes.
SSD recovery feasibility by failure scenario below
When you delete a file on an SSD, the operating system sends a TRIM command telling the controller which LBAs (logical block addresses) are no longer needed. The controller marks those pages as invalid in its flash translation layer (FTL). The physical NAND cells are not erased at this point.
Most modern SSDs implement DRAT or DZAT (Deterministic Read After TRIM / Deterministic Zeroes After TRIM), which means the controller immediately returns zeroes when those addresses are read through the normal interface, even though the underlying NAND cells still hold their original charge. The actual physical erasure happens later during garbage collection, asynchronously.
Once a TRIM command is fully processed, the controller intentionally blocks access to the deleted files through standard interfaces. Unless the drive suffered an immediate hardware failure before TRIM executed, the data is permanently unrecoverable through conventional software.
This is the opposite of how hard drives work. On a spinning disk, deleted files sit untouched until new data overwrites them. On a TRIMmed SSD, the data becomes inaccessible through the controller within seconds of deletion. Physical NAND erasure follows during garbage collection, but the controller will not serve the data from the moment TRIM completes.
The distinction that matters: if you deleted files and the drive kept running, TRIM has already done its job and those blocks are logically unmapped. If the drive died from a hardware failure (dead controller, shorted PMIC, firmware corruption), the data may still exist on the raw NAND.
On modern drives with hardware-level encryption (virtually all contemporary NVMe and many SATA SSDs use Self-Encrypting Drive technology by default), the decryption keys are tied to the controller. If the controller is permanently dead and cannot be revived through firmware repair or component-level microsoldering, extracting the raw NAND yields only unreadable ciphertext. Recovery in these cases depends entirely on restoring controller functionality, not on chip-off NAND extraction.
DZAT and DLFEAT: How Controllers Block Access to TRIMmed Data
SATA SSDs that support DZAT (Deterministic read ZEROs After TRIM) immediately return zeroes to any read request targeting TRIMmed logical block addresses. NVMe SSDs use a separate mechanism: the Deallocate command paired with the DLFEAT (Deallocate Logical Block Features) field in the drive's namespace metadata. When DLFEAT reports 001b, the controller returns all zeroes for deallocated blocks.
This zeroing happens at the controller's protocol layer before garbage collection physically erases the underlying NAND cells. Even if the original voltage charges remain on the floating gates for minutes or hours after deletion, the controller refuses to serve that data through any standard interface. Software tools see only zeroes.
Drives that support deterministic zeroing (such as the Samsung 860/870 SATA families and the 980 NVMe series) make software-based undelete after TRIM or Deallocate impossible; the controller enforces the deletion at the protocol level, independent of the physical state of the NAND cells.
Not all SATA SSDs support DZAT. Older drives with DRAT (Deterministic Read After TRIM) return a fixed, consistent payload for TRIMmed addresses, which may or may not be zeroes. Budget controllers with non-deterministic TRIM may return unpredictable data patterns. DZAT is required on enterprise and NAS-optimized SATA SSDs for RAID parity consistency.
On the NVMe side, the vast majority of modern NVMe SSDs enforce deterministic zeroes (DLFEAT=001b) upon deallocation. In all deterministic cases, once TRIM or Deallocate executes, the data is inaccessible from any software perspective. The only scenario where TRIMmed data might be recoverable is when the controller died before completing the TRIM operation, leaving the NAND pages intact in their pre-TRIM state.
TRIM on Windows
Windows enables TRIM automatically on any SATA or NVMe SSD using native Microsoft drivers. The Storage Optimizer (formerly Disk Defragmenter) schedules a weekly "Retrim" pass that re-issues TRIM commands for all previously deleted blocks, ensuring the controller stays current even if the initial TRIM was missed. On a healthy Windows system, deleted data is typically logically unmapped and rendered inaccessible within seconds of deletion during normal use, and any stragglers are caught by the next weekly Retrim cycle.
TRIM on macOS
On Macs with a T2 chip (late 2017 through 2020, starting with the iMac Pro) or Apple Silicon (M1/M2/M3/M4), every byte written to the internal SSD is encrypted by default using AES-256 in XTS mode, with keys managed by the Secure Enclave inside the SoC. This encryption is always-on and transparent; you do not need to enable FileVault for it to be active. When files are deleted, macOS sends a standard TRIM command, and the controller handles it like any other SSD: the LBAs are marked invalid in the FTL and reads return zeroes. The Secure Enclave does not destroy any keys in response to individual file deletions.
What makes T2/M-series recovery different is not TRIM behavior; it is the always-on hardware encryption tied to the specific SoC. Because every block on the NAND is AES-256 encrypted with keys that exist only inside the Secure Enclave on that specific chip, desoldering the NAND yields only ciphertext regardless of whether TRIM has run. Chip-off is useless on these machines. The only recovery path when the logic board is dead is board-level microsoldering to get the Secure Enclave operational again so it can decrypt in place. We will not accept payment for a case we know cannot succeed.
Crypto-shredding, where the Secure Enclave destroys the volume encryption key and makes all data on the drive permanently irrecoverable, happens only during a full disk erase (Erase All Content and Settings, or a DFU restore). That operation is instant and absolute. It is distinct from per-file TRIM, which leaves the encryption keys intact.
On older Macs without a T2 chip using third-party SSDs, TRIM is not enabled by default. Users must run sudo trimforce enable to activate it. Until that command is run, deleted files persist on the NAND and standard recovery applies.
TRIM on Linux
Linux TRIM behavior depends entirely on the distribution and file system. Many distros batch TRIM commands via a weekly fstrim.timer service, creating a window where deleted data remains on the NAND before the timer executes. However, modern setups (such as Btrfs) increasingly default to asynchronous real-time discard, which unmaps blocks in the background continuously. If real-time discard is active, the data is unmapped immediately and is unrecoverable through the controller.
Write Amplification and Garbage Collection
TRIM tells the controller which blocks are free. Garbage collection is what the controller does with that information: it consolidates valid pages from partially-empty blocks into new blocks, then erases the old ones to create clean write targets. This runs continuously in the background whenever the drive is powered on and idle. Every consolidation cycle means extra writes to the NAND that the host never requested. That ratio of actual NAND writes to host writes is called write amplification. A drive with a write amplification factor of 3x wears its cells three times faster than the host workload alone would suggest. Heavy random writes, a nearly full drive, and aggressive garbage collection all push the factor higher, accelerating the path toward ECC failure and controller lockup.
The practical takeaway: if your SSD died from a hardware failure and never had the chance to run garbage collection after the crash, the metadata in the service area is likely intact, giving us a strong chance to reconstruct the FTL. If the drive was running for days in a degraded state, grinding through garbage collection cycles before it finally locked up, the controller may have already damaged the service area beyond repair. The sooner a failing drive is powered off and sent to a lab, the better.
SSD Recovery Feasibility by Failure Scenario
| Operational Condition | Encryption Status | Physical / Logical State | Recovery Feasibility |
|---|---|---|---|
| TRIM enabled (NTFS, APFS) | Unencrypted | Logical deletion | Near zero; controller has zeroed the blocks |
| TRIM enabled (exFAT, FAT32) | Unencrypted | Logical deletion | Moderate; these file systems issue TRIM less aggressively |
| TRIM disabled or not issued | Unencrypted | Logical damage | High; NAND retains all data |
| TRIM disabled or not issued | Encrypted (key available via working controller) | Logical damage | High; decrypt in place, then image |
| TRIM disabled or not issued | Encrypted (key unknown or lost) | Any state | Zero; no viable decryption path |
| Any TRIM state | Any encryption | Severe physical damage (dead controller) | Depends on board repair feasibility; TRIM cannot execute on a dead controller |
TRIM cannot execute on a physically dead controller. If the drive died from a hardware failure before the OS sent TRIM commands, deleted data is still on the NAND.
Which SSD Form Factors and Interfaces Can Be Recovered?
We recover data from SATA 2.5-inch, M.2 NVMe, and M.2 SATA form factors. Each uses a different protocol and controller architecture, requiring distinct PC-3000 modules and adapter hardware for firmware-level diagnostic access and NAND imaging.
SATA (2.5-inch)
SATA SSDs use the same AHCI protocol as spinning hard drives, capped at 600 MB/s. Controllers from Samsung (MEX/MJX), Silicon Motion (SM2259), and Phison (S12) follow well-documented architectures, common in laptops and desktops. Phison S11 controllers are the most common source of SATAFIRM S11 firmware failures. PC-3000 supports these natively over a standard SATA port; no adapters required.
M.2 and NVMe
M.2 is a physical connector shape, not a protocol. An M.2 slot can carry either SATA or NVMe. NVMe drives communicate over the PCIe bus with multi-queue command sets that reach 7,000+ MB/s on Gen 4 hardware. Recovery requires the PC-3000 Portable III with its dedicated PCIe SSD adapter; the tool issues low-level vendor commands over PCIe lanes to force controllers into safe/diagnostic mode, load custom firmware, and read NAND directly. Standard USB enclosures cannot do this.
NAND Cell Architecture and Degradation
Data Retention Warning: Unlike magnetic hard drives, SSDs do not hold data indefinitely when powered off. While solid-state storage is reliable, data can eventually degrade if the drive is left unpowered for years. Drives that have endured heavy write activity (exhausting their rated endurance) are particularly vulnerable to charge leakage and can begin losing data in as little as a year if stored in warm environments without power. If your SSD fails, do not leave it in a drawer for months before seeking recovery; the charge in the NAND cells will leak, leading to uncorrectable bit errors.
As NAND flash cells degrade through program/erase cycles, their voltage distributions widen and the margins between states shrink. The controller compensates using error correction (LDPC or BCH), but once bit errors exceed the ECC threshold, the controller cannot resolve the page. If the corrupted pages sit in the service area where the firmware and flash translation layer (FTL) live, the controller loses its map of where data is stored. The drive drops offline and reports 0 bytes or fails to enumerate entirely. The NAND still holds the data; the controller has lost the ability to find it.
At that point, PC-3000 forces the failed controller into diagnostic mode (Techno Mode), injects a working firmware loader, and rebuilds the translator from NAND metadata. For drives with severe NAND degradation or charge retention loss, we apply controlled heat to shift voltage thresholds back into readable range; a technique demonstrated in our NVMe recovery walkthrough.
What Does the SSD Recovery Process Look Like Step by Step?
SSD recovery follows five stages: current profiling to identify shorts, safe mode access to prevent garbage collection, translator rebuilding to reconstruct the NAND address map, multi-pass imaging with adjusted read parameters, and file system extraction to a target drive.
Every SSD that arrives at our Austin lab goes through these diagnostic and repair stages. The specific path depends on the failure type, but the workflow is consistent.
- Current Profiling: We connect the SSD to a bench power supply with current limiting and measure draw at 5V (2.5" SATA) or 3.3V (M.2 NVMe). A healthy SSD draws minimal current at idle but shows initialization spikes when it tries to load firmware. A shorted PMIC or controller pulls well above normal and shows as a hot spot on our FLIR thermal camera within seconds. This tells us whether the failure is a short circuit (needs component replacement) or a firmware/logical issue (needs PC-3000).
- Safe Mode Access (ROM Mode / Pin Shorting): A failing NVMe or SATA controller left to power up normally will attempt to load its corrupted firmware and may execute background garbage collection, permanently erasing NAND blocks flagged by prior TRIM commands. To prevent this, we physically isolate the controller from the NAND by shorting specific Vout or clock pins on the PCB before applying power.
This forces the controller into a minimal ROM mode (called "Techno Mode" on Phison, "Factory Access Mode" on Samsung, "Test Mode" on Silicon Motion) where it accepts commands but does not execute autonomous background tasks.
Once in ROM mode, PC-3000 Portable III uploads a custom microcode loader directly into the controller's SRAM. This loader replaces the corrupted on-NAND firmware with a minimal instruction set that enables stable, single-channel read access to the flash. With the loader active, the controller responds to vendor-specific commands without running garbage collection, wear leveling, or TRIM execution, preserving every NAND block in its current state for imaging.
- Translator Rebuilding: PC-3000 scans raw NAND metadata to reconstruct the flash translation layer (FTL), which maps logical addresses to physical NAND pages. Without this map, the drive cannot locate any files. The rebuild process reads spare area bytes from every NAND page to piece together the correct logical-to-physical mapping.
- Multi-Pass Imaging: Using PC-3000 Data Extractor, we image the SSD sector by sector. Sectors that fail on the first pass get queued for retry with adjusted read parameters. For degraded NAND, we apply thermal stabilization to shift voltage thresholds into a readable range. The result is a sector-by-sector clone on a target drive.
- File System Extraction: We mount the cloned image, verify file integrity, and transfer recovered data to the customer's choice of media. The original failed SSD is returned or securely retired per the customer's instructions.
How Does Hardware Encryption Affect SSD Recovery?
Hardware encryption ties the decryption key to the controller silicon. When the controller fails, desoldering the NAND yields only AES-256 ciphertext. Recovery requires board-level repair of the original controller so it can decrypt in place; chip-off extraction is not viable on encrypted drives.
The controller generates the key on first use, stores it internally, and encrypts every write transparently. When the drive functions normally, you never notice. When the drive fails, encryption determines whether chip-off recovery is even possible.
Self-Encrypting Drives and TCG Opal
Drives that comply with the TCG Opal specification store the media encryption key (MEK) internally, typically wrapped by a Key Encryption Key (KEK). On modern NVMe controllers, this KEK is cryptographically bound to unique, irreversible hardware fuses or a Physically Unclonable Function (PUF) inside the specific controller silicon that shipped with the drive. If the controller dies, simply swapping it for a matching replacement will not work because the donor IC will lack the unique hardware key required to unwrap the MEK. In these cases, chip-off recovery is also impossible, as the raw NAND contains only AES-256 ciphertext. Recovery relies entirely on our ability to perform component-level repair on the original board: fixing power rails or replacing PMICs so the original controller can power up and decrypt its own storage.
BitLocker and FileVault
BitLocker (Windows) and FileVault (macOS) add a software encryption layer on top of the drive. Recovery requires the original password, recovery key, or TPM chip. If you have the recovery key, we image the drive and decrypt offline. If the key is lost and the TPM chip is on a dead motherboard, the motherboard itself needs repair to release the key. We handle both the drive-side and board-side work.
Apple T2 and M-series
Apple solders NAND directly to the logic board and ties the encryption key to the Secure Enclave inside the T2 chip (late 2017 through 2020 Macs, starting with the iMac Pro) or the M-series SoC (2020 onward). The NAND cannot be read without the Secure Enclave on the same board. If the logic board dies, the encryption key is inaccessible unless the board is repaired at the component level. Chip-off is useless here; the raw NAND is AES-256 encrypted with a key that exists nowhere else. The only recovery path is logic board microsoldering to get the board powered on so the Secure Enclave can decrypt in place. We documented one such case where a MacBook SSD that shorted and smoked required full board-level repair before the Secure Enclave could decrypt.
Bottom line: on any hardware-encrypted drive, desoldering the NAND without the original encryption key produces unreadable data. Board-level repair to restore the original controller or security chip is the only path that preserves the decryption chain. This is why microsoldering capability matters for SSD recovery; not every lab has it.
Which SSD Controller Failures Are Most Common?
Certain SSD controllers have well-documented failure patterns tied to specific firmware bugs, power-loss behavior, or NAND management decisions. Phison E12 drives die after power interruptions mid-cache-flush. Silicon Motion SM2262EN controllers enter a locked read-reject state after SLC cache corruption. Samsung 980 Pro drives brick from a firmware 0E health bug. All are recoverable through PC-3000 diagnostic mode when the controller silicon is intact.
If your drive uses one of the controllers below, the symptoms listed will be familiar.
Phison E12 Sudden Death
The Phison PS5012-E12 controller (found in Corsair MP510, Sabrent Rocket, Inland Premium, and Team MP34) has a known failure mode where the controller locks up after a power loss event. The drive drops out of BIOS entirely or reports 0 bytes. The FTL stored in the SLC cache region gets corrupted because the controller was mid-write when power was cut. PC-3000 forces the E12 into Vendor Specific Command mode, bypasses the corrupted SLC cache, and rebuilds the translator from the TLC main area.
Silicon Motion SM2262EN Firmware Lock
The SM2262EN (used in HP EX950, ADATA SX8200 Pro original revision, and Kingston KC2000) is a DRAM-equipped NVMe controller. When the host system crashes during a write, the controller enters a locked state where it responds to SMART queries but refuses all read/write commands. The drive appears in BIOS with correct capacity but is inaccessible. We use PC-3000's Silicon Motion NVMe utility to clear the lock flag, inject a clean firmware loader, and rebuild the mapping tables from NAND spare area data.
Samsung 980 Pro 0E Error
Samsung 980 Pro drives with the Elpis controller develop a firmware bug that causes the 0E health indicator to degrade rapidly, eventually bricking the drive. Samsung issued firmware patches, but drives that were not updated in time die with the controller stuck in a write-protect state. PC-3000's Samsung NVMe module can issue Vendor Specific Commands to override the write-protect flag and image the drive before the controller locks out permanently.
WD Blue SA510 / SN580 Firmware Panic
The WD Blue SA510 (SATA) and SN580 (NVMe) use SanDisk in-house controllers with proprietary firmware. Both models exhibit a failure pattern where the drive enters a firmware panic state after an unexpected power loss or sustained thermal stress. The drive stops enumerating entirely or reports 0 bytes. These controllers rely on Low-Density Parity-Check (LDPC) error correction with proprietary parameters in the controller's firmware. Because the LDPC decode parameters are controller-specific, desoldering the NAND and reading it with a flash reader produces data that cannot be decoded without the original controller's ECC engine. Recovery requires forcing the controller into its factory diagnostic mode via PC-3000 and rebuilding the flash translation layer without reinitializing the NAND.
SandForce SF-2281 Cryptographic Lockout
The SandForce SF-2281 controller (found in older Kingston HyperX, Corsair Force GT, and Intel 520 Series drives) performs always-on AES-128 encryption on all data written to NAND, even when the user has not set a password. (The SF-2281 was marketed as AES-256, but Intel confirmed in 2012 that the AES-256 implementation was broken at the silicon level; only AES-128 functions correctly.) The media encryption key is stored inside the controller IC itself. When the SF-2281 enters a permanent BSY (busy) state from firmware corruption or a power event, the controller stops responding to all commands. The NAND contains only ciphertext that cannot be decrypted without the original controller. Chip-off recovery is not viable. SF-2281 recovery requires specialized proprietary techniques to clear the panic state, restore controller communication, and image the drive while the encryption chain remains intact.
InnoGrit IG5236 "MN-5236" Firmware Panic
The InnoGrit IG5236 (codenamed Rainier) is an 8-channel Gen4 NVMe controller with onboard DRAM, found in the ADATA XPG Gammix S70 Blade, HP FX900 Pro, Acer Predator GM7000, and Mushkin Redline Vortex. When the controller encounters a defective NAND page or suffers a firmware exception during a sustained mixed workload, it drops its programmed identity and reverts to the silicon's default descriptor: "MN-5236" with a reported capacity of 2MB or 2.1GB. The drive may also trigger KERNEL_DATA_INPAGE_ERROR blue screens before going silent.
The IG5236 implements AES-256 hardware encryption, so desoldering the NAND from a panicked board yields only ciphertext. Recovery requires forcing the controller into its factory diagnostic mode, halting background operations, and reconstructing the corrupted FTL from surviving NAND metadata. Because the encryption keys are bound to the controller silicon, the original IG5236 must remain operational throughout imaging. A separate failure pattern occurs after power loss: the controller enters a 30+ second recovery cycle on the next boot. If the user power-cycles during this window, the FTL corruption compounds and the drive becomes permanently undetectable without specialized firmware-level intervention.
NVMe Controller Recovery: How We Access Failed Gen3 and Gen4 Drives
NVMe controller recovery requires forcing the controller into a diagnostic mode before it can load its corrupted firmware and execute background garbage collection. Each controller family (Phison, Silicon Motion, Samsung) has a distinct diagnostic entry point and vendor-specific command set. Using the wrong entry sequence causes the controller to proceed with normal boot, triggering the corruption that makes recovery harder.
Below is how we approach the three most common NVMe controller families using PC-3000 Portable III with its dedicated PCIe SSD adapter. A Phison E18 does not respond to the same vendor commands as a Samsung Elpis or a Silicon Motion SM2262EN.
Phison E18 and E12: Clearing Firmware Panics on Gen4 and Gen3 NVMe
The Phison PS5018-E18 (Corsair MP600 Pro, Sabrent Rocket 4 Plus, Seagate FireCuda 530, Kingston KC3000) is an 8-channel Gen4 controller with triple ARM Cortex-R5 cores and 4th-generation LDPC error correction. When thermal stress or power loss corrupts the FTL during a cache flush, all three cores fail to boot past the corrupted service area modules. The drive disappears from BIOS entirely.
We short specific pins on the PCB to prevent the controller from loading its on-NAND firmware, forcing it into a minimal ROM state that PC-3000 recognizes as the Phison NVMe diagnostic interface. From there, the Phison NVMe Active Utility uploads a custom microcode loader into the controller's SRAM, replacing the corrupted boot sequence with a stripped-down instruction set. This loader enables single-channel NAND reads without executing garbage collection, wear leveling, or TRIM. Because the E18 implements AES-256 hardware encryption with TCG Opal 2.0, chip-off is not viable; the NAND contains only ciphertext. The entire recovery depends on keeping the original controller operational.
The older Phison PS5012-E12 (Gen3; Corsair MP510, Sabrent Rocket, Inland Premium) follows a similar workflow but with a simpler dual-core architecture and fewer firmware modules to reconstruct.
Silicon Motion SM2262EN and SM2269XT: Resolving Lock States on NVMe Drives
The SM2262EN (ADATA SX8200 Pro, HP EX950, Kingston KC2000) uses dual ARM Cortex-R5 cores with onboard DRAM. Both the SM2262EN and the DRAM-less SM2269XT (found in Solidigm P41 Plus, ADATA Legend 850) enter a strict locked state when NAND wear-leveling thresholds are exceeded or when an SLC cache flush is interrupted mid-operation. The drive appears in BIOS with correct model and capacity but rejects all read and write commands.
PC-3000's Silicon Motion NVMe utility pushes the controller into Technological Mode by uploading a specialized loader directly into the controller's RAM through vendor-specific PCIe commands. Once in Technological Mode, the controller halts all autonomous background operations and exposes raw NAND access. We read the spare area bytes from every NAND page to reconstruct the logical-to-physical address map that the corrupted FTL can no longer provide. ADATA's silent swap from SM2262EN to the slower SM2262G in later SX8200 Pro production runs means controller identification is mandatory before selecting the correct recovery module.
The SM2269XT stores its mapping tables in Host Memory Buffer rather than onboard DRAM, making it more vulnerable to FTL corruption from system crashes. The same Technological Mode workflow applies, but the corrupted state is more severe because no local DRAM copy of the translator survives the power loss.
Samsung Elpis and Phoenix: Bypassing Firmware Lockouts on Samsung NVMe
The Samsung Elpis (980 Pro, PM9A1 OEM) is fabricated on Samsung's 8nm process, while the older Samsung Phoenix (970 EVO, 970 EVO Plus) uses a 14nm process. Both are Samsung's proprietary NVMe controllers with hardware-bound AES-256 encryption where the media encryption key is fused into the controller silicon. Desoldering the NAND from an Elpis or Phoenix board yields only ciphertext; there is no external key to apply.
The Elpis controller's known 0E firmware bug (firmware 3B2QGXA7, primarily on 2TB models) forces the drive into a permanent write-protect state. Samsung released a patch (5B2QGXA7), but drives that were not updated in time require recovery. We use the PC-3000 Samsung NVMe module to issue Vendor Specific Commands that override the write-protect flag, then image the drive sector by sector while the controller's own hardware ECC engine handles NAND error correction. The controller must remain alive throughout; if it dies during imaging, the encryption keys die with it.
Phoenix controller failures on the 970 EVO typically present as complete non-detection after a power event. PC-3000 forces the Phoenix into Factory Access Mode, a diagnostic state that bypasses the normal firmware boot sequence and allows direct NAND reads through the controller's intact decryption pipeline. The drive is imaged in this state without ever loading the corrupted production firmware.
SATA SSD Controller Recovery: Phison, Silicon Motion, and Marvell Workflows
SATA SSD recovery uses PC-3000 SSD over a standard SATA port to force the controller into a diagnostic mode that halts background operations and exposes raw NAND access. Phison, Silicon Motion, and Marvell controllers each require distinct ATA Vendor Specific Command sequences to enter that mode. Using the wrong sequence or cycling power before safe mode is confirmed risks triggering garbage collection on worn cells, compounding the corruption.
Unlike NVMe controllers that communicate over PCIe lanes, SATA controllers use the AHCI protocol, which simplifies the hardware interface but does not simplify the firmware repair. Below is how we approach the three most common SATA controller families.
Phison PS3111-S11: Translator Table Reconstruction
The Phison PS3111-S11 (Kingston A400, Patriot Burst, PNY CS900) is a single-core SATA controller that stores its flash translation layer in a dedicated service area region across the NAND. When power cuts during a service area write, the translator tables corrupt. The drive reports as "SATAFIRM S11" or "PATA SSD" with 0 bytes capacity because the controller reverts to its silicon default identity.
PC-3000 SSD connects to the drive over SATA and uses the Phison SSD Utility to issue ATA Vendor Specific Commands that place the controller into Safe Mode. In Safe Mode, the PS3111 halts all autonomous operations and exposes raw NAND access. The utility scans every NAND chip for surviving service area copies; Phison controllers maintain two redundant copies of the translator (called "Map Table A" and "Map Table B"). If either copy is intact, the utility loads it and the drive re-enumerates with correct capacity. If both copies are damaged, PC-3000 rebuilds the translator by reading the spare area bytes from each NAND page and reconstructing the logical-to-physical address map from scratch. This full rebuild is the most time-intensive scenario and falls into the $600–$900 firmware recovery tier.
The PS3111 does not implement hardware-level encryption by default, so chip-off NAND extraction remains a viable last resort if the controller silicon is physically destroyed.
Silicon Motion SM2258 and SM2259H: Partial Page Read and FTL Recovery
The Silicon Motion SM2258 (ADATA SU800, Team CX2), SM2258XT (Crucial BX500, ADATA SU650), and SM2259H (Crucial MX500) are SATA controllers with dual-core ARM processors. The SM2258 and SM2259H include onboard DRAM for FTL caching; the SM2258XT is the DRAM-less variant that relies on Host Memory Buffer (HMB). When these controllers encounter an unrecoverable ECC error in the service area during boot, they enter a locked state where the drive responds to SMART queries but refuses all read/write commands. The drive appears in BIOS with correct model and capacity yet remains inaccessible.
PC-3000 SSD's Silicon Motion SATA utility pushes the controller into Technological Mode by issuing a specific ATA Vendor Specific Command sequence through the SATA port. Once in Technological Mode, all background processes stop and raw NAND access opens. For drives with degraded NAND where standard reads return ECC failures, the utility performs partial page reads: it reads each NAND page at multiple voltage reference points and selects the read that produces the lowest raw bit error rate. This is distinct from PC-3000's thermal-assisted reads used for NVMe; partial page reads adjust the electrical sensing margins digitally rather than using physical temperature changes. The SM2258 and SM2259H (DRAM-equipped) typically recover faster because a local DRAM copy of the translator often survives a power event. The SM2258XT (DRAM-less) lacks this buffer, and its FTL corruption is more severe after a system crash.
Marvell 88SS1074: Firmware Corruption and Test Pad Recovery
The Marvell 88SS1074 (Crucial MX300, Plextor M8V) is Marvell's mainstream SATA controller with a proprietary firmware structure. The 88SS1074 uses a tri-core ARM Cortex-R5 architecture with Marvell's NANDEdge LDPC error correction engine. The most common failure pattern is a firmware exception during a background media management operation (garbage collection or wear leveling), which leaves the controller in a boot loop: it repeatedly attempts to load its firmware, fails, and resets. The drive appears intermittently in BIOS or drops out after a few seconds of enumeration.
PC-3000 SSD's Marvell utility accesses the controller through a factory diagnostic interface. On the 88SS1074, the entry point is a specific test pad on the PCB that must be shorted to ground during power-on to force the controller into ROM Boot Mode. In ROM Boot Mode, the controller does not load any firmware from NAND; it waits for external commands over the SATA interface. PC-3000 uploads a diagnostic loader into the controller's internal SRAM, which provides stable NAND access without executing the corrupted production firmware. The utility then reconstructs the flash translation layer from the NAND spare area and images the drive.
The 88SS1074 supports AES-256 encryption, though many consumer drives ship with it disabled at the firmware level. When encryption is active, chip-off produces ciphertext and recovery depends entirely on reviving the original controller through board-level repair.
Why Do Consumer SSDs Fail Without Warning?
Consumer NVMe and SATA SSDs omit the tantalum supercapacitors found in enterprise drives. Those capacitors provide 10 to 50 milliseconds of backup power, long enough for the controller to flush its DRAM cache and finalize the flash translation layer (FTL) to NAND. Without them, a power cut mid-write leaves the FTL partially written, corrupting the logical-to-physical address map.
On the next power cycle, the controller cannot locate any data. The drive reports 0 bytes, shows the wrong model string, or fails to enumerate entirely. The data is still in the NAND; the map that points to it is broken.
DRAM-less Drives Are More Vulnerable
Budget NVMe controllers like the Phison E21T, Silicon Motion SM2263XT, and Maxio MAP1602 use Host Memory Buffer (HMB) instead of onboard DRAM. The FTL mapping tables live in your computer's system RAM, allocated by the NVMe driver.
A system crash, BSOD, or hard reboot deallocates that memory before the controller can write its state back to NAND. The result is identical to a power loss: corrupted FTL, unreadable service area, and a drive that appears dead. DRAM-equipped controllers like the Phison E18 or Samsung Elpis keep a local copy of the mapping table in their onboard SRAM/DRAM, which provides a fractional-second buffer during power transitions. This does not make them immune, but it reduces the window of vulnerability from milliseconds to microseconds.
SLC Cache Flush Interruption
Modern TLC and QLC SSDs use a pseudo-SLC write cache: incoming data lands in NAND cells programmed to a single bit per cell (fast, high endurance), then the controller folds that data into TLC/QLC pages (three or four bits per cell) during idle periods. If power drops during this folding operation, the data exists in two conflicting states across different physical NAND pages. The FTL metadata no longer matches the actual NAND contents. On Phison controllers, this manifests as a Vendor Specific Command (VSC) lockout where the controller refuses all read/write operations until the inconsistency is resolved. PC-3000 resolves this by reading raw NAND metadata from both the SLC cache region and the TLC/QLC main storage, identifying which copy is authoritative, and rebuilding the translator from scratch.
Windows 11 24H2 and Host Memory Buffer Crashes
Windows 11 version 24H2 changed how the operating system allocates Host Memory Buffer (HMB) for NVMe SSDs. The updated driver expanded the default HMB allocation from 64MB to as much as 200MB. On certain DRAM-less controllers whose firmware expects the smaller allocation, this larger memory footprint causes firmware instability under sustained I/O. The primary victims are WD Black SN770 and WD Blue SN580 drives, whose proprietary in-house controllers are hardcoded for a 64MB HMB ceiling. Other DRAM-less controllers (Phison E21T, Silicon Motion SM2263XT) have shown isolated issues, though the WD models account for the majority of confirmed failures. Symptoms range from repeated BSOD (KERNEL_DATA_INPAGE_ERROR, CRITICAL_PROCESS_DIED) to the drive vanishing from BIOS entirely after the update.
The NAND flash and your data are intact in these cases. The controller's FTL metadata corrupts because the host OS deallocates the expanded HMB region mid-operation, leaving the mapping tables in a partially written state. Rolling back the Windows update can prevent further damage but cannot restore a corrupted FTL. Recovery requires bypassing the host interface entirely and accessing the controller through its factory diagnostic mode to extract data before the corrupted mapping tables are overwritten by further boot attempts. If your DRAM-less NVMe SSD stopped working after a Windows update, do not reformat or reinstall the OS on the same drive; send it for evaluation.
Unpowered Storage and Charge Leakage
NAND flash cells store data as trapped electrical charge on a floating gate (planar NAND) or a charge trap layer (3D NAND). That charge leaks over time. The JEDEC JESD218B specification defines client SSD data retention as one year at 30 degrees Celsius for a drive at end of rated endurance.
A drive stored in a hot environment, an attic, a parked car, or a non-climate-controlled storage unit, leaks charge faster. Worn cells that have consumed most of their rated program/erase cycles leak faster still. As charge leaks, the voltage distributions for each programmed state shift and overlap. QLC cells, which encode four bits across sixteen voltage levels, have the tightest margins and degrade first. TLC cells with three bits across eight levels follow.
When voltage distributions overlap beyond the controller's ECC correction threshold (LDPC on modern drives, BCH on older ones), pages become unreadable through the normal interface. PC-3000's Read Retry feature applies shifted reference voltages during reads, effectively recalibrating the sensing margins to account for the charge drift. For drives with severe retention loss, controlled heating of the NAND package temporarily improves charge distribution separation, allowing marginal pages to be read before the thermal energy dissipates.
Practical takeaway: if a failed SSD has been sitting unpowered in a drawer for months, send it to a lab sooner rather than later. Every week of unpowered storage at room temperature narrows the voltage margins further. A drive that is recoverable today may not be recoverable in six months.
Which SSD Manufacturers Can Be Recovered?
We recover data from Samsung, Crucial, Western Digital, Intel, ADATA, SK Hynix, Kioxia, Corsair, Kingston, Seagate, and Apple proprietary SSDs. Each manufacturer uses different controller architectures, firmware structures, and encryption implementations that require manufacturer-specific PC-3000 recovery modules and vendor command sequences.
- Samsung
- 870 EVO (SATA), 970/980/990 NVMe families. Proprietary controllers (Phoenix/Elpis/Pascal) and default encryption are common. The 990 Pro firmware degradation bug is a frequent case; controller repair and safe imaging for all Samsung models.
- Crucial / Micron
- MX500 (SM2258/SM2259H), BX500 (SM2258XT), P2 (SM2263XT), P3/P3 Plus (Phison E21T), P5 Plus (Micron DM02A1). Silicon Motion, Phison, and Micron controller recovery. Enterprise Micron SSDs (5400, 7450, 9400).
- Western Digital / SanDisk
- WD Blue/Black (e.g., SN750, SN850X with firmware 620311WD lockout), SanDisk Extreme portable with hardware encryption/USB bridge failures; repair controller/bridge or transplant NAND while preserving keys.
- Intel / Solidigm
- 545s (SM2259), 660p (SM2263 QLC), 670p (SM2265), 760p (SM2262), Solidigm P41 Plus (SM2269XT). Intel-custom firmware on Silicon Motion controllers.
- ADATA / XPG
- SX8200 Pro (SM2262EN/SM2262G), SU800 (SM2258), SU650, Legend 800 (RTS5772DL), Legend 960 Max, Gammix S70 Blade (IG5236). Silicon Motion, Realtek, and InnoGrit controller recovery.
- SK Hynix
- Gold P31 (ACNT038), Platinum P41 (ACNS075), Gold S31 (SH87830CC). Proprietary controller recovery. Distinct from Intel/Solidigm.
- Kioxia / Toshiba
- Exceria (Phison E12C), Exceria Pro (Phison E18), Exceria Plus G3 (E21T). Legacy Toshiba RC500, XG5, XG6, OCZ. BiCS FLASH NAND. Phison module recovery via PC-3000.
- Corsair
- MP600 PRO (Phison E18), MP700 (Phison E26 Gen5), MP600 Mini (E21T 2230), MP510 (E12). All Phison controllers; PC-3000 SSD Phison module recovery.
- Kingston, Seagate & Others
- A2000/KC2500/NV2, FireCuda 520, and more. Realtek/Phison/SMI variants handled in-house with PC-3000.
- Apple Proprietary & T2/M-series
- Older Apple blade SSDs via adapters; T2/M-series require logic-board repair to access integrated, encrypted storage. See MacBook Data Recovery.
Find Your SSD Controller
Recovery approach depends on the controller chip inside your SSD. We track failure modes for every major controller family.
SSD Diagnostic Guides
Specific failure scenarios with technical explanations and what to do next.
SSD Shows 0GB or Wrong Capacity
Controller firmware panic; do not format
Can You Recover Data After TRIM?
When TRIM erases are permanent and when they are not
SSD vs HDD Recovery: What's Different
No cleanroom, no head swap; firmware and micro-soldering
NVMe vs SATA Recovery Differences
Protocol, encryption, and chip-off considerations
Does Data Recovery Void My Warranty?
Magnuson-Moss Act and what “authorized” actually means
Specific SSD Failure Modes & Recovery Techniques
Firmware Corruption Recovery
SATAFIRM S11, 0GB capacity bugs, and translation layer failures fixed with PC-3000 firmware tools; not canned software.
Learn moreChip-Off & NAND Flash Extraction
When the controller is dead beyond repair, we desolder NAND chips and reconstruct your data from raw flash; with honest limits on encrypted drives.
Learn moreNVMe & PCIe SSD Recovery
M.2 NVMe drives fail differently than SATA SSDs. Thermal throttling, PCIe lane failures, and controller burnout require specialized diagnostic workflows.
Learn moreThe Cleanroom Myth for SSDs
SSDs have no spinning platters. Any lab charging you cleanroom fees for SSD work is padding the bill.
Learn moreRossmann vs. DriveSavers
Transparent pricing and board-level repair vs. $3,000+ "call for quote" bait-and-switch. See the real numbers.
Learn moreDoes Data Recovery Void Your Warranty?
Short answer: no. The Magnuson-Moss Warranty Act protects you, and we explain exactly how.
Learn moreReal SSD Recovery Case Studies
Watch unedited video of actual SSD recoveries: controller repairs, firmware rebuilds, NAND extractions. 2.49M+ YouTube subscribers watch these.
Learn moreNAND Thermal Stabilization
Degraded NAND cells need precise temperature control to shift read thresholds. We use targeted thermal manipulation through PC-3000 to recover sectors that fail at room temperature.
Learn moreMicrosoft Surface SSD Recovery
Early Surface Pro and Go models use soldered NAND behind adhesive-sealed screens. Newer Pro models and Surface Laptops use removable M.2 2230 drives, but access still requires specialized disassembly.
Learn moreSanDisk Extreme Firmware Failure
Class-action design flaw in SanDisk Extreme and Extreme Pro Portable SSDs. Defective solder joints and R332G190 firmware cause sudden total data loss. USB bridge bypass and PC-3000 recovery.
Learn moreMacBook-Specific SSD Recovery
Apple T2 Chip Data Recovery
Late 2017 through 2020 Macs (starting with the iMac Pro) use the T2 chip for SSD encryption. When the logic board fails, board-level repair is the only path to your data.
Learn moreLogic Board Swap vs. Data Recovery
A replacement logic board has different encryption keys. Board repair preserves data; board replacement destroys it.
Learn moreM1/M2/M3/M4 Soldered NAND Recovery
On Apple Silicon Macs, SSD storage is soldered to the logic board and paired to the processor. Recovery requires board-level component repair.
Learn moreSSD Data Recovery FAQs
Can you recover data from a dead SSD?
How much does SSD data recovery cost?
How much does NVMe data recovery cost?
Is SSD data recovery harder than hard drive recovery?
Can encrypted SSDs be recovered?
What's your success rate for SSD recovery?
Why is my SSD showing 0 bytes?
Why does my SSD show up as SATAFIRM S11?
Can deleted files be recovered from an SSD?
Does the freezer trick work on SSDs?
How long does SSD data recovery take?
Can data be recovered from an SSD not detected in BIOS?
What causes SSD controller failure?
Can you recover data from a water-damaged SSD?
Do you recover data from Apple T2 or M-series Macs?
Is chip-off recovery possible on encrypted SSDs?
Can I recover SSD data myself with software?
What is the difference between logical and physical SSD failure?
Should I keep powering on a failing SSD?
My laptop SSD failed. How do I get my data?
My portable SSD stopped working. What happened?
Can you recover a Samsung 970 or 980 EVO/Pro?
Can an SSD be repaired?
What determines the cost of SSD data recovery?
Is SSD repair the same as SSD data recovery?
Will a firmware update fix a dead SSD?
Does SSD data recovery require a cleanroom?
Is NVMe SSD recovery different from SATA SSD recovery?
Can deleted files be recovered from an external USB SSD?
What does MN-5236 mean on my SSD?
Did the Windows 11 24H2 update kill my SSD?
Does running CHKDSK fix a failing SSD?
Does the SSD power cycle method work?
How do I know which SSD data recovery price tier applies to my drive?
What board-level repairs fix a dead SSD?
Does the SSD controller type affect the recovery cost?
Why did my files disappear after running CHKDSK on my SSD?
Why does my SATA SSD recovery approach differ from NVMe recovery?
What to do before shipping
These steps protect the NAND and reduce the risk of further damage before we receive the drive.
Do NOT:
- Stop using the drive immediately; don't write new data
- Do not open the SSD; leave any corrosion/contamination to us
Do:
- Pack in an anti-static bag with padding; include your contact info
- Use tracked shipping to our Austin lab; request signature on delivery
- Provide passwords/keys if the volume is encrypted
Secure Mail-In from Anywhere in the US
1 Business Day
FedEx Priority Overnight delivers to Austin by 10:30 AM the next business day from most US addresses.
- New York City 1 Business Day
- Los Angeles 1 Business Day
- Chicago 1 Business Day
- Seattle 1 Business Day
- Denver 1 Business Day
Fully Insured
Use FedEx Declared Value to cover hardware costs. We return your original drive and recovered data on new media.
Packaging Standards
- ✓Use the box-in-box method: float a small box inside a larger box with 2 inches of bubble wrap.
- ✓Wrap the bare drive in an anti-static bag to prevent electrical damage.
- ✗Do not use packing peanuts. They compress during transit and allow heavy drives to strike the edge of the box.
Nationwide Mail-In Data Recovery Service
We serve all 50 states with secure mail-in data recovery. Ship your failed drive to our Austin lab using our free shipping kit, and we'll diagnose it within 24-48 hours. No geographic limitations—we've successfully recovered data for customers from Alaska to Florida.
Popular Service Areas
Sources & References
Technical claims and specifications on this page are sourced from public documentation. Verify independently.
- ACE Lab PC-3000 Portable III: Manufacturer documentation for SSD recovery capabilities, including PCIe/NVMe adapter support, vendor-specific safe mode commands, firmware loader injection, and NAND flash direct reading. This is the primary diagnostic and imaging tool used in our lab.
- JEDEC JESD218B: Solid-State Drive Requirements and Endurance Test Method: Industry standard defining SSD endurance testing, NAND flash data retention periods, and program/erase cycle specifications. Client SSD data retention is defined as 1 year at 30°C; enterprise is 3 months at 40°C.
- Magnuson-Moss Warranty Act (15 U.S.C. §2302): Federal law establishing that manufacturers cannot void a warranty for using an independent repair provider. Relevant to customers concerned about warranty status after third-party data recovery.
- Competitor pricing ranges are based on published customer reports and competitor pricing pages as of early 2025. DriveSavers, Ontrack, and Secure Data figures reflect publicly available quote ranges, not internal data.
Ready to get your data back?
Free evaluation. No data = no charge. Mail-in from anywhere in the U.S.